Question
a.
a
b.
b
c.
c
d.
d
Posted under Cryptography and Network Security
Engage with the Community - Add Your Comment
Confused About the Answer? Ask for Details Here.
Know the Explanation? Add it Here.
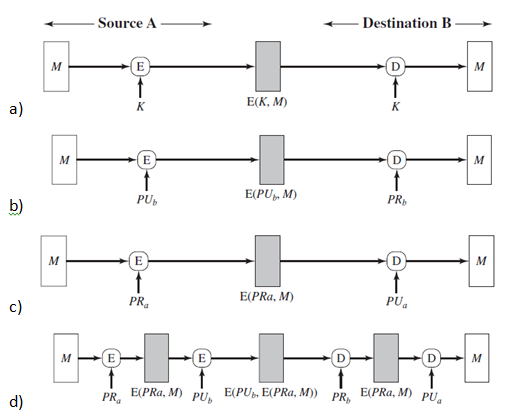
Q. Which figure implements confidentiality and authentication?
Similar Questions
Discover Related MCQs
Q. Which figure implements confidentiality, authentication and signature?
View solution
Q. The below figure implements authentication and signature only?
View solution
Q. The below figure represents internal error control.
View solution
Q. The following figure has authentication tied to the plain text-
View solution
Q. What does the following figure represent?
View solution
Q. What does the below figure represent?
View solution
Q. Another name for Message authentication codes is
View solution
Q. For a 150-bit message and a 10-bit MAC, how many values are the MAC value dependent on?
View solution
Q. Confidentiality can only be provided if we perform message encryption before the MAC generation.
View solution
Q. MACs are also called
View solution
Q. For a 100 bit key and a 32 bit tag, how many possible keys can be produced in the 3rd round?
View solution
Q. MAC is a
View solution
Q. For an n-bit tag and a k-bit key, the level of effort required for brute force attack on a MAC algorithm is
View solution
Q. Cryptographic hash functions execute faster in software than block ciphers.
View solution
Q. What is the value of ipad in the HMAC structure?
View solution
Q. What is the value of opad in the HMAC structure?
View solution
Q. Which cryptographic algorithm is used in CMAC?
View solution
Q. In CMAC, which scenario is a different key K2 is used instead of K1?
View solution
Q. Which Authentication Encryption approach is taken by the SSL/TLS protocol?
View solution
Q. Which Authentication Encryption approach is taken by the IPSec protocol?
View solution
Suggested Topics
Are you eager to expand your knowledge beyond Cryptography and Network Security? We've curated a selection of related categories that you might find intriguing.
Click on the categories below to discover a wealth of MCQs and enrich your understanding of Computer Science. Happy exploring!








